Building a Next-Generation Cyber Defense with Frontier AI: A Practical Guide
Introduction
In the rapidly evolving landscape of cybersecurity, frontier artificial intelligence (AI) is no longer a distant concept—it’s a critical battlefield asset. Recent breakthroughs from labs like OpenAI, Anthropic, and Google DeepMind, combined with proven platforms such as SentinelOne’s AI-native defense, demonstrate that the future of cyber defense lies in autonomous, machine-speed operations. This guide walks you through a practical, step-by-step approach to integrate frontier AI into your cybersecurity strategy—whether you’re a security operations center (SOC) manager, a CISO, or a tech lead. You’ll learn how to assess your current defenses, adopt behavioral AI, automate threat response, and stay ahead of zero-day exploits and supply chain attacks like those seen with LiteLLM, Axios, and CPU-Z. Let’s turn the promise of frontier AI into a concrete defense plan.
What You Need
- Access to frontier AI models (via partnerships or APIs from OpenAI, Anthropic, or Google DeepMind)
- An AI-native security platform (e.g., SentinelOne or equivalent that supports behavioral AI and autonomous response)
- Integration capabilities for endpoint, cloud, identity, data, network, and AI attack surfaces
- A skilled cybersecurity team familiar with AI/ML concepts and incident response
- Real-time threat intelligence feeds and vulnerability databases
- Testing environment (sandbox) to validate AI-driven responses without disrupting production
- Data governance policies to ensure compliance when using AI for security analysis
Step-by-Step Guide
Step 1: Assess Your Current Security Posture and Identify Gaps
Before integrating frontier AI, map your existing defenses across all attack surfaces—endpoints, cloud, identity, data, network, and any AI-based assets. Use a framework like MITRE ATT&CK to catalog your detection and response capabilities. Pay special attention to zero-day vulnerabilities and supply chain risks (e.g., compromised trust in third-party tools). Determine where your current tools rely on manual analysis or signature-based detection, as these are the areas where AI-native automation can provide the biggest leap. Also, quantify the speed of your response: human-driven SOCs often take minutes to hours, while machine-speed AI can act in milliseconds. This baseline will help you measure progress.
Step 2: Establish Partnerships with Frontier AI Labs
Follow the example of companies like SentinelOne that have long collaborated with OpenAI, Anthropic, and Google DeepMind. Seek formal partnerships or developer access programs to gain early insights into model capabilities (e.g., advanced reasoning over attack paths, vulnerability discovery). While specifics may be confidential, even limited access allows you to test how frontier models can enhance your security operations. Build an internal evaluation pipeline—feed real-world threat data (anonymized) to the models and measure their accuracy in identifying malicious behavior versus false positives. Document these findings to justify further investment.
Step 3: Integrate Behavioral AI and Autonomous Response
Deploy an AI-native platform that uses behavioral AI—not just static rules—to detect anomalies. Configure it to operate at machine speed without human intervention for known malicious patterns. For example, when a zero-day exploit is attempted (like those in the LiteLLM supply chain attack), the system should automatically isolate the affected endpoint, block the process, and initiate a rollback. Use the platform’s built-in automation to cover endpoint, cloud, identity, and network layers. Ensure the AI can reason about attack paths: if a vulnerability is found in one component, the system should assess if it’s exploitable in your live environment (since many bugs are not meaningful in practice). This prioritization is key.
Step 4: Implement Continuous Learning from Frontier Model Evolution
Frontier AI models are constantly improving. Establish a process to regularly update your defense AI with new learnings from frontier labs. This includes not only new model versions but also insights into how attackers use AI to find vulnerabilities faster. For instance, as frontier models become better at identifying software bugs (like those leading to the Axios and CPU-Z attacks), your defense must correspondingly improve at autonomous patch management and virtual patching. Create a feedback loop where incidents (both successes and near-misses) are used to retrain your behavioral models. Use the two distinct examples from SentinelOne’s experience: supply chain attacks often exploit unpatched zero-days, and only a machine-speed autonomous response can block them in time.
Step 5: Prioritize Real-World Risk Over Raw Vulnerability Counts
One major lesson from frontier AI is that not all discovered vulnerabilities are exploitable in your environment. Use AI-powered reasoning to correlate vulnerability data with your specific architecture, runtime protections, and mitigation layers. Filter out “theoretical” bugs that are already blocked by existing controls (e.g., ASLR, CFG). Focus your AI on operational risk—for example, a zero-day in a publicly exposed API is higher priority than one in an internal tool with limited blast radius. Your automation should be tuned to stop actual attacks, not to chase every CVE. This aligns with the principle that many vulnerabilities are reduced by architectural layers, and raw counts rarely map to real-world risk.
Step 6: Test and Refine Through Supply Chain Attack Scenarios
Run tabletop exercises using examples like the LiteLLM, Axios, and CPU-Z incidents. Simulate a scenario where a trusted agent or workflow is compromised (a key vector in the AI era). Your AI-native defense should detect the anomalous behavior—e.g., a trusted library making unusual network connections—and respond autonomously. Measure the time from detection to containment. If your system takes longer than a few seconds, refine the AI’s decision threshold and automate additional response actions. Repeat these drills regularly to ensure your team trusts the autonomous actions. Also, evaluate how your AI handles false positives: in a high-stakes environment, you want to minimize alert fatigue while still catching zero-days.
Step 7: Scale Protection Across All Attack Surfaces
Expand your AI-native defense to cover not only endpoints but also cloud workloads, identity systems, data stores, network traffic, and AI-specific attack surfaces (like model poisoning). Use a unified platform that provides a single console, leveraging frontier AI to correlate telemetry from all sources. For example, if a phishing email reaches an employee’s inbox (identity/email surface), the AI should automatically block the malicious link and then scan for similar patterns across the network. The goal is to create a self-defending ecosystem that adapts to novel threats without human intervention. This is what the original text calls “the value of that approach only grows” as frontier AI advances.
Tips for Success
- Start small, scale fast. Begin with one attack surface (e.g., endpoints) and prove the value of AI-native defense before expanding.
- Maintain human oversight for complex decisions. Even the best frontier AI can make mistakes—keep a human-in-the-loop for high-impact actions (e.g., shutting down critical servers).
- Invest in data quality. AI is only as good as the data it trains on. Clean, labeled telemetry from real attacks is invaluable.
- Collaborate with other defenders. Share anonymized threat intelligence with peers and frontier labs to improve collective defense (as seen in SentinelOne’s partnerships).
- Stay agile. Attackers also use AI—monitor the latest research on adversarial AI and update your models accordingly.
- Think beyond vulnerability counts. Focus on stopping actual attacks, not patching every theoretical bug.
- Review and update your response playbooks. AI automation should be continuously fine-tuned based on post-incident reviews.
- Ensure compliance. When using AI for security, document data handling, bias checks, and decision logs for audit purposes.
By following these steps, you can build a cyber defense that leverages the full potential of frontier AI—just as advanced platforms like SentinelOne have demonstrated. The race between attackers and defenders will only intensify, but with a machine-speed, AI-native approach, you can stay one step ahead.
Related Articles
- Two Decades of Cyber Turmoil: 20 Pivotal Events That Redefined Digital Security
- Supply Chain Attack on Popular ML Tool Exposes User Credentials
- British Hacker Behind Tech Giants Phishing Spree Pleads Guilty
- CISA Flags Critical Linux Privilege Escalation Flaw Under Active Attack
- Meta Unveils Major Security Upgrades for Encrypted Backups: Fleet Key Distribution and Transparency Initiative
- Cracking the Code: A Practical Guide to Defeating Traveling Key Locks
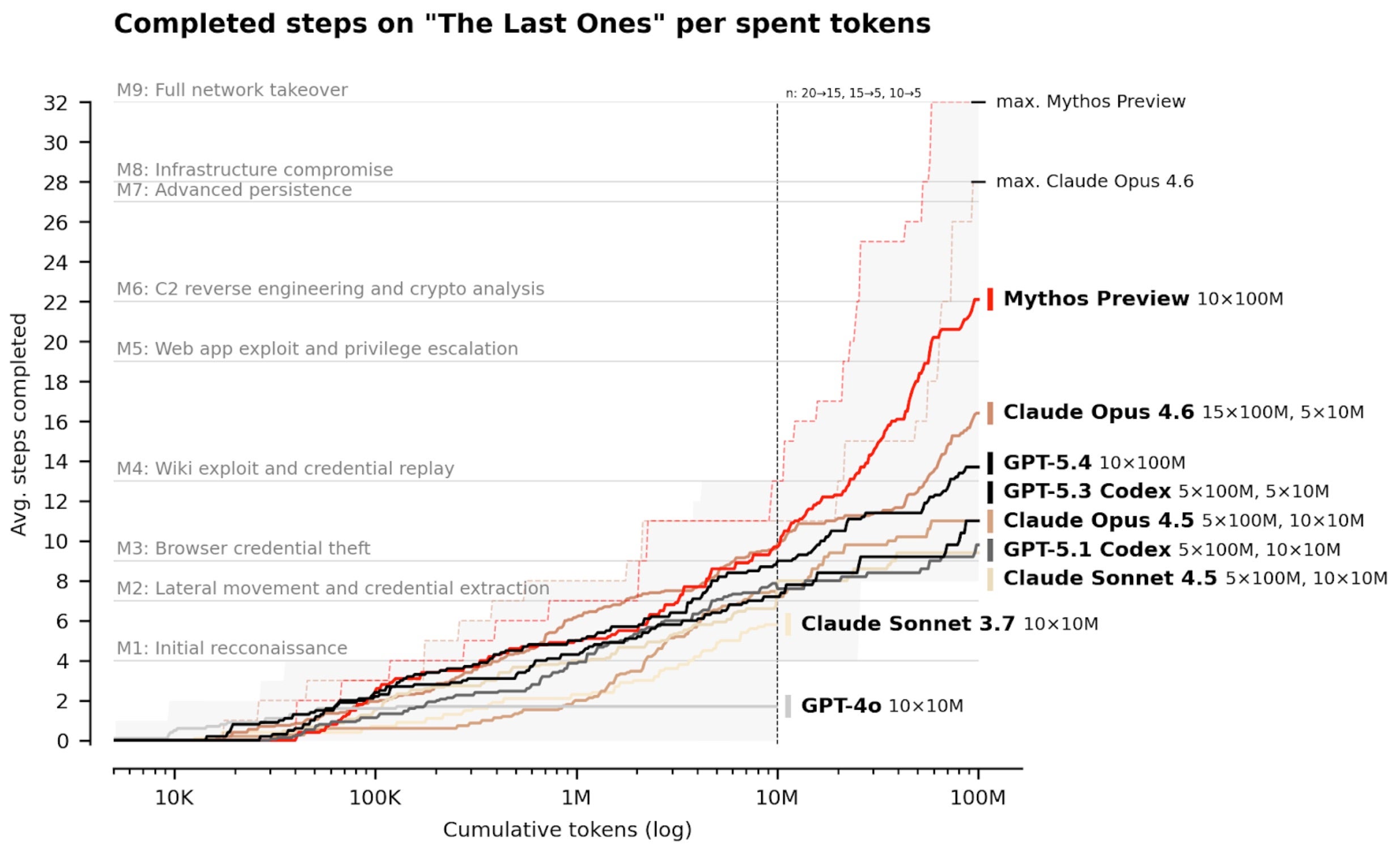
- 6 Key Insights on Anthropic's Mythos and the Future of Cybersecurity
- The AI Gateway Supply Chain Attack: How Malicious Code Stole Credentials and Crypto Data